Microsoft has recently implemented a significant architectural change in SharePoint Online and Microsoft Teams, allowing us to now consume and collaborate with User-defined RMS protected files. But what does this mean, and how can it simplify our organization’s ability to collaborate securely with sensitive information? Historically, files protected with custom permissions could only be opened using locally installed Office applications, and collaborative editing was not feasible. This limitation hindered collaboration on highly sensitive data and mandated that all parties have a local Office installation.
While we still rely on locally installed Microsoft 365 apps like Word, PowerPoint, and Excel for encryption, the introduction of Custom permissions empowers users to determine who has access and the level of access for specific documents or presentations. These permissions can be assigned to internal users, groups, as well as external users and entire organizations. Consider the following examples where sensitive information needs protection:
- Read-only rights for everyone at an external law firm.
- Full rights for the management team by assigning them to an existing group.
- Editing rights for an external board member.
The user can now select the appropriate sensitivity level and define custom permissions.
The user can now select the appropriate sensitivity level and define custom permissions.
When selecting Custom Permission in the current M365 apps, users must navigate to More Options to precisely configure permissions for users, groups, or domains.
A glimpse into the future is provided by the M365 Beta channel design, offering a clearer and more intuitive interface for defining Custom Permission.
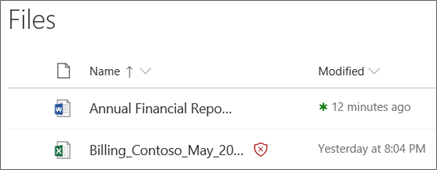
With these new capabilities, files can now be saved and shared via OneDrive/SharePoint/Teams, preventing unauthorized downloads and enabling simultaneous access and editing by multiple users.
For instance, an external user opening the file via Word Online will be restricted from downloading, copying, or printing it. Our system does not require any applications from counterparts, ensuring data security by blocking file downloads.
From an encryption/decryption standpoint, this marks a significant paradigm shift. Encryption using this feature is currently limited to locally installed M365 apps; thus, Teams and web apps cannot be used to protect these files, and are solely intended for consumption.
This is still significant news for several organizations that have been waiting to offer this capability to their business. We can now offer collaboration while still tightly controlling who accesses the information and with what rights. With this online support, we provide the ability to share and collaborate on this document without requiring software from our counterpart. Files can now be opened via any web browser for editing or consumption. We get protection that always follows the file wherever it is stored, with all access logged and controlled through Microsoft Enter ID.
As always, it’s imperative to have robust processes in place for managing encrypted data. User-defined permissions necessitate even higher standards, particularly during offboarding procedures. Therefore, it’s essential to review and refine these procedures before expanding encryption capabilities.


























 Sensitivity label settings for Teams meetings and chats
Sensitivity label settings for Teams meetings and chats